![]() Bitcoin Design
Bitcoin Design
Slideshow
Edit
1. Alex frames the trust problem at checkout
2. Alex proposes replacing trust with proof
3. Ownership as a chain of signatures
4. Why valid signatures still aren’t enough
5. Why a central checker defeats the purpose
6. Public announcement and one agreed history
7. Timestamping with hash-linked records
8. Proof-of-work makes ordering expensive to fake
9. Majority CPU power becomes the voting system
10. Why confirmations make reversal unlikely
11. How the network converges in real time
12. Alex’s closing description of Bitcoin
Motivation & Setup
1. Alex frames the trust problem at checkout
Alex is prepping a lunch-and-learn, and he opens by telling the team that most online payments lean on trusted intermediaries to approve, arbitrate, and sometimes reverse transactions. He stresses how this safety net adds fees, delays, minimum payment sizes, and a constant worry for merchants delivering instant or non-returnable services.
2. Alex proposes replacing trust with proof
Alex tells them his goal for the session is simple: imagine payments that work between two willing parties without needing a bank-like referee. Instead of trusting an institution, the system should make fraud expensive and honesty easy to verify, so the confidence comes from cryptographic evidence and shared rules rather than corporate policy.
Transactions & Ownership
3. Ownership as a chain of signatures
Alex explains that a “coin” can be treated like a history of handoffs: each owner authorizes the next transfer by signing a compact fingerprint of the prior handoff together with the next owner’s public key. The recipient can then verify every signature in order and see a clean lineage of who was allowed to spend at each step.
4. Why valid signatures still aren’t enough
Alex pauses and points out the trap: two different recipients could both receive perfectly valid signature chains for the same coin if the spender cheated. Signatures prove authorization, not uniqueness, so without a shared view of which spend happened first, both victims may believe they were paid until they learn a conflicting transaction existed.
5. Why a central checker defeats the purpose
Alex describes the obvious fix—a central mint that checks every spend and rejects duplicates—but he warns it recreates the same dependency the team is trying to escape. If one operator must bless every transaction, that operator becomes a bottleneck, a surveillance point, and a single failure that can be attacked, coerced, or mismanaged.
Consensus & Timestamping
6. Public announcement and one agreed history
Alex says the real breakthrough is social and technical at once: transactions must be broadcast publicly, and the network must converge on one ordering of events so everyone agrees which spend was first. If the group can settle on a single history, later conflicting spends can be rejected consistently, and payees can rely on inclusion as evidence.
7. Timestamping with hash-linked records
Alex explains a timestamping approach: bundle recent transactions, take a hash as a compact commitment, and publish it so everyone can see what existed by that time. Each new published record includes the previous record’s hash, forming a chain where tampering with earlier data would change every later link, making alteration obvious and costly.
Proof-of-Work & Security
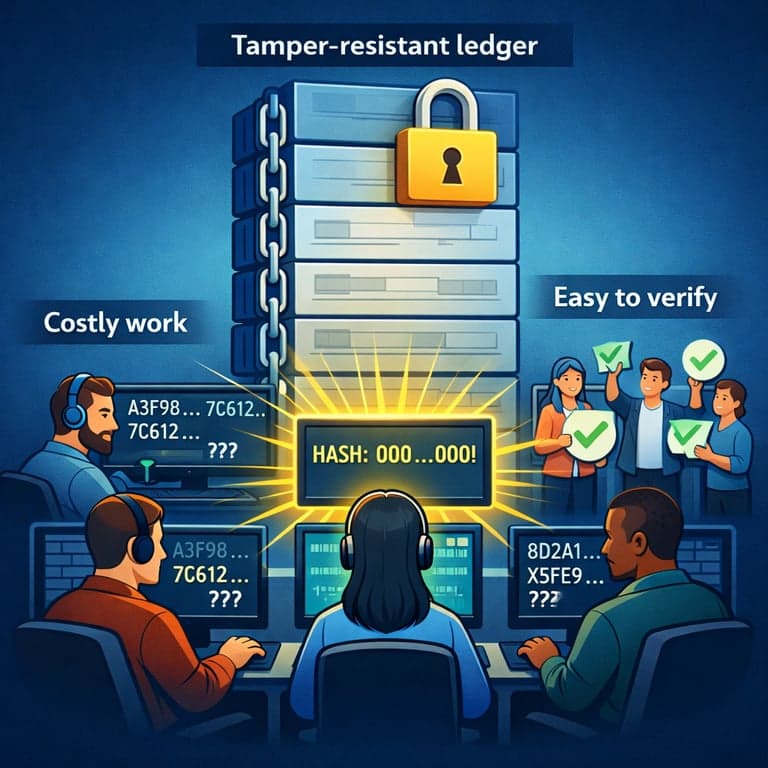
8. Proof-of-work makes ordering expensive to fake
Alex introduces proof-of-work as the mechanism that turns timestamps into a robust public ledger. Nodes compete to find a nonce that makes a block hash meet a difficulty target, and while the search is costly, checking a winning block is cheap. This imbalance means rewriting history requires redoing massive work, not just telling a lie.
9. Majority CPU power becomes the voting system
Alex tells the team that proof-of-work acts like voting weighted by real-world resource expenditure rather than identity. The chain with the most cumulative work represents the strongest claim to “what happened,” because honest participants extend it faster. As long as honest nodes control the majority of compute, their history tends to dominate competing versions.
10. Why confirmations make reversal unlikely
Alex describes what it would take to reverse a payment: an attacker must rebuild the block containing it and every block after, then catch up to and surpass the honest chain. With each additional block added on top, the attacker falls further behind unless they have overwhelming compute, so waiting for more confirmations steadily increases practical finality.
Network Operation
11. How the network converges in real time
Alex walks through day-to-day operation: transactions are broadcast, nodes validate them, assemble candidate blocks, and race to solve proof-of-work. When a block is found, others accept it if valid and build on its hash. If two blocks appear at once, nodes temporarily split but then switch to whichever branch accumulates more work first.
Wrap-up
12. Alex’s closing description of Bitcoin
By the end, Alex summarizes confidently: Bitcoin is a decentralized, timestamped ledger where ownership transfers are verified by signatures, and double-spends are prevented by public broadcast plus consensus on a single history. Proof-of-work makes that history costly to rewrite, and majority honest CPU power keeps the shared record coherent without a trusted gatekeeper.