![]() Solana Concepts
Solana Concepts
Slideshow
Edit
1. Alex Opens With the Clock Problem
2. A Clock You Can Audit
3. Proof of History as a Hash Clock
4. Stamping Events Into the Timeline
5. Sequential to Produce, Parallel to Verify
6. Timing Intuition With Simple Formulas
7. Keeping Generators Honest With Back-References
8. Checkpoint Overhead as a Practical Trade
9. Leader–Verifier Pipeline for Execution
10. PoH Shrinks Coordination for Fast Finality
11. Proof of Stake: Votes Backed by Bonds
12. Leader Rotation and Failure Handling
13. Partition Recovery and Liveness Tradeoffs
14. Throughput Claims From Wire Math
15. Compute and Memory as the Other Limits
Motivation
1. Alex Opens With the Clock Problem
Alex, the junior engineer, tells the team that distributed nodes only trust their own local time, so timestamps can’t safely decide which transaction came first. Without a shared clock, the network must trade many messages to agree on order under adversarial conditions, raising latency and making fast confirmation difficult as participation grows.
2. A Clock You Can Audit
Alex frames the goal as a public ordering signal that doesn’t require trusting peers: something anyone can check later to infer “this happened before that” and roughly how much time elapsed. He emphasizes that reducing coordination is the real win, because coordination is what slows consensus when the network is large and noisy.
Proof of History
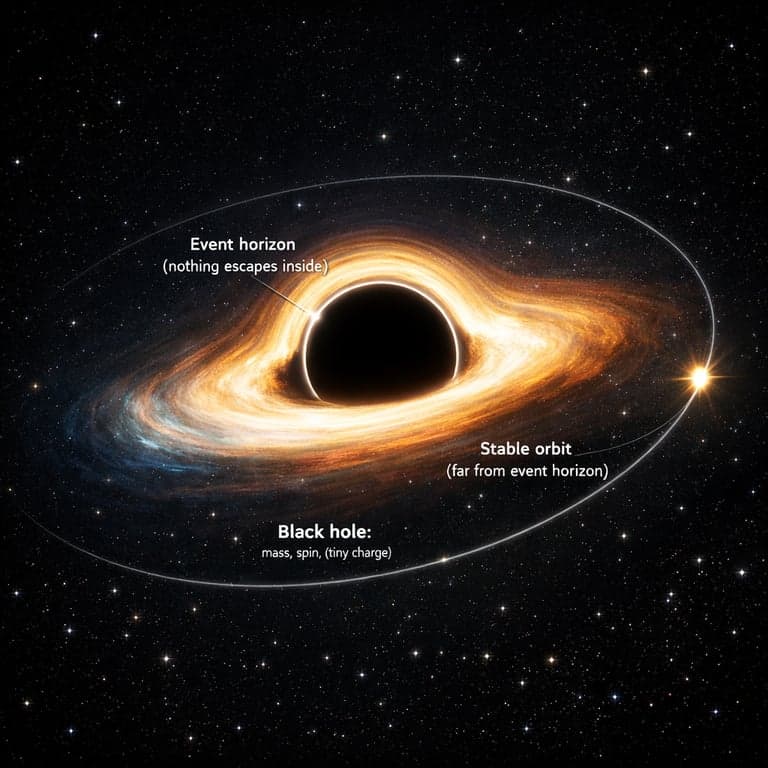
3. Proof of History as a Hash Clock
Alex introduces Proof of History as a sequence where each hash depends on the previous one, forcing strictly sequential production. Because you can’t jump ahead without doing the work, the position in the chain becomes a cryptographic tick. The team sees how publishing checkpoints lets anyone verify progress without trusting the producer.
4. Stamping Events Into the Timeline
Alex explains that transactions or event hashes are mixed into the current PoH state so the next hash commits to that insertion. Once recorded, every later hash depends on it, fixing the event’s relative placement in the timeline. His takeaway: ordering becomes provable after the fact, not negotiated in real time.
5. Sequential to Produce, Parallel to Verify
Alex points out the twist: generating the PoH stream is single-threaded by design, but verification is parallel. Verifiers split the published sequence into slices, recompute each slice independently, and check boundary hashes match. With GPU cores verifying many slices at once, audit speed scales while the clock stays tamper-evident.
6. Timing Intuition With Simple Formulas
Loading equations
Security & Attacks
7. Keeping Generators Honest With Back-References
Alex warns that a malicious producer might try to hide an alternate history with reordered events. To constrain that, clients include the latest PoH hash they observed as a back-reference, and can sign the event plus reference. When the ledger is checked, any event referencing a nonexistent or later hash is rejected as inconsistent.
Performance
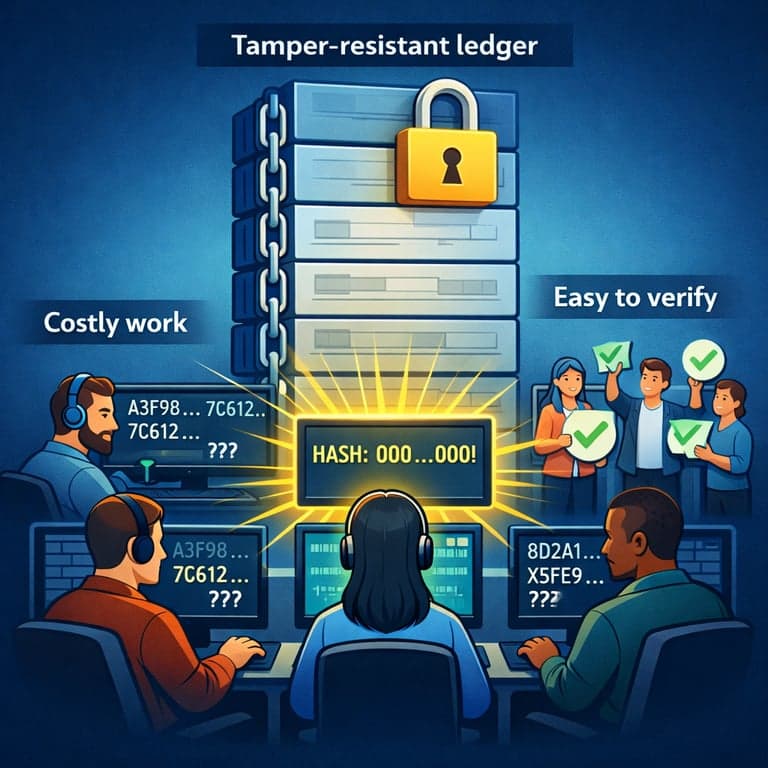
8. Checkpoint Overhead as a Practical Trade
Alex describes the cost side: frequent PoH checkpoints consume bandwidth and require verification compute. He argues the design aims for “expensive to fake, cheap to check,” so the network can afford tight consensus loops. The team notes that the overhead is predictable engineering, not an open-ended coordination tax.
System Architecture
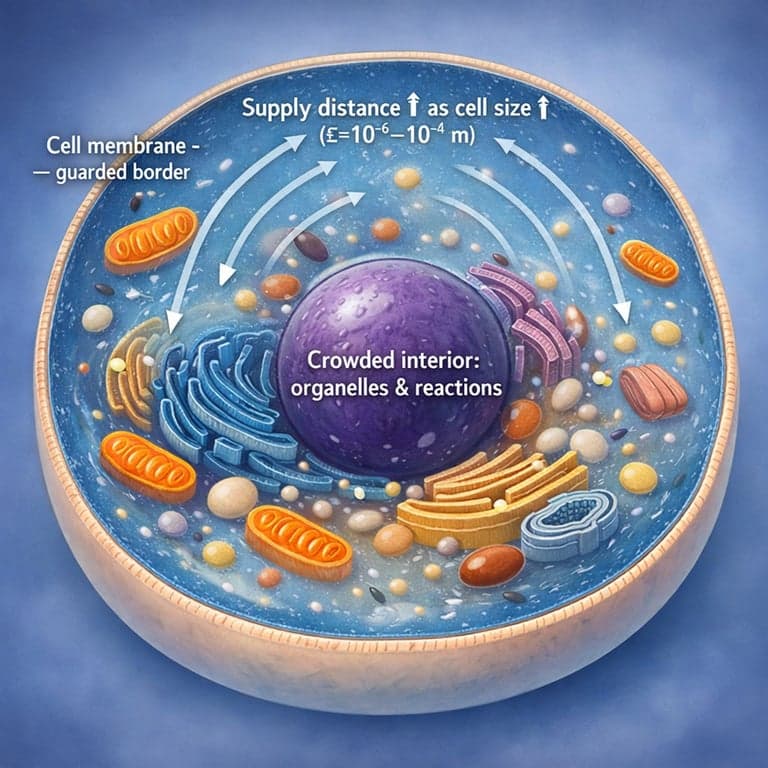
9. Leader–Verifier Pipeline for Execution
Alex walks through the workflow: a Leader builds the PoH stream, orders incoming user transactions for efficient execution, runs them against a RAM-resident state, then emits signed state hashes after batches. Verifiers replay the same ordered transactions locally and publish their own signed state hashes, turning execution correctness into something the network can confirm.
Finality & Timing
10. PoH Shrinks Coordination for Fast Finality
Alex explains that PoH lets everyone audit when transactions and votes appeared relative to the timeline, even if they didn’t witness the gossip live. With objective ordering, validators can follow strict vote deadlines and the network can prove whether they met them. The result is fewer round trips spent arguing about “who saw what when.”
PoS Consensus
11. Proof of Stake: Votes Backed by Bonds
Alex connects the timeline to incentives: validators lock stake as bonds to gain voting weight and sign confirmations for the Leader’s state hash at particular PoH positions. A supermajority of bonded stake finalizes a branch, and slashing punishes equivocation or signing invalid state. He stresses this ties fast confirmation to economic cost, not goodwill.
12. Leader Rotation and Failure Handling
Alex describes how the system replaces a failing Leader when timeouts, exceptions, or identity conflicts appear. The next Leader is selected by voting power, and must gather a fresh supermajority of confirmations on its sequence. He also notes the idea of a secondary path for quicker handover, reducing downtime during planned or forced transitions.
13. Partition Recovery and Liveness Tradeoffs
Alex explains that when the network partitions, missing votes gradually become “stale,” and stake can be dynamically treated as inactive after enough missed opportunities. If participation is high, the system recovers quickly; if not, progress slows to give humans time to decide which side to trust. He frames it as a deliberate safety–liveness balance.
Performance
14. Throughput Claims From Wire Math
Loading equations
15. Compute and Memory as the Other Limits
Alex adds that signature checks are embarrassingly parallel, so GPUs can validate large numbers of signatures per second, while a large RAM state reduces disk bottlenecks. He describes the design philosophy: keep execution and verification close to hardware limits, and use PoH ordering plus replay to keep the network aligned without constant negotiation.